Advertising kompromat from cyber espionage companies
In 2021, Jeffrey Burrill, an American Catholic priest and general secretary of the American Bishops’ Conference, resigned from his position in the church. Reason? Catholic media outlet The Pillar published information that the priest violated the commandment of celibacy, as he allegedly used gay apps on his phone and visited gay bars and bathhouses. But how did the media actually get the information with which it compromised the priest? Well, this is where the story just begins.
The priest’s data has been obtained from commercially available databases. The Pillar obtained commercially available data on his use of gay dating apps, as well as his cell phone location data and browsing habits, revealing that he visited gay bars and gay baths.
Identifying sinners with technology. Source: »Europe’s hidden security crisis« report, 2023.
The data has been obtained from the RTB (Real-Time Bidding) system. This is, simply put, an online advertising system that enables the automated buying and selling of advertising space in real time. However, this system primarily enables precise targeting of advertising campaigns. Namely, advertisers can direct ads to very precisely defined groups of people, according to the desired demographics, location, their behavioural data, etc. Many big tech companies like Google, Facebook, Amazon, Microsoft, etc. offer their RTB systems to advertisers, and anyone can buy the access to these data as an advertiser. But more on that a little bit later.
It turned out that this incident was not an isolated case at all. Behind this kind of spying on Catholic priests has been the conservative Catholic organization Catholic Laity and Clergy for Renewal, which invested as much as 4 million dollars in checking whether Catholic priests adhere to the commandment of celibacy. And those who were found to have sinned, were publicly nailed to the cross through the media. It took 52 weeks of RTB data to identify Jeffrey Burrill, and his fate has been sealed.
Collection of online advertising data
The RTB system categorizes individuals on the basis of various data, but roughly speaking, it is an extensive collection of demographic data (which includes gender, age, education, occupation, as well as information about family status, etc.), data about user behavior online (search history, clicks,…), individual purchasing habits, location data (we always carry our phones with us!), data about the user’s devices (smartphone, tablet or computer brand, operating system and web browser,…) and much more.
Extensive user segmentation is then carried out in the background based on the collected data. The system classifies users into various categories, such as “Industry - Manufacturing - Aerospace and Defense”, “Family member of an employee in the military”, “Civil servant - elected official”, and of course also “Television journalist” or “Cleric”. Each of these categories can then be further divided into subcategories based on their interests, behavioural patterns, demographic data, etc.
Would you like to show an ad to all municipal administration employees in Slovenia who are female, between 20 and 30 years old and frequently visit websites about healthy food? No problem. With a few clicks, your targeted ad will reach exactly this group of users. What if you wanted to show your ad to priests from France who visit gay websites and are under the age of 40? As we have seen, this is not a problem either.
There is no doubt that RTB data is very useful for advertisers. But on the other hand, it is clear that they contain very sensitive information about individuals, including location data, what they read, watch or listen to online, what their sexual interests are, etc. And from the collected data it is also possible to infer their personal problems.
What about anonymity?
The next question is, of course, how anonymous this data actually are? Advertisers claim that they are, since the data is anonymized, so it is practically impossible to identify specific individuals with them.
But the truth is much simpler. Researchers from the University of Washington in 2017 has shown, that for just US$1,000 they can monitor the physical movements of a specific individual and the use of sensitive mobile applications (for example, those that indicate an individual’s religion or sexual orientation) with these advertising data. In the article Exploring ADINT: Using Ad Targeting for Surveillance on a Budget - or - How Alice Can Buy Ads to Track Bob, researchers Paul Vines, Franziska Roesner and Tadayoshi Kohno asked themselves a simple research question: “Can a third party obtain private information about specific individuals by buying online ads?”. And they came to unanimous answer: yes, it is definitely possible. And not too complicated either.
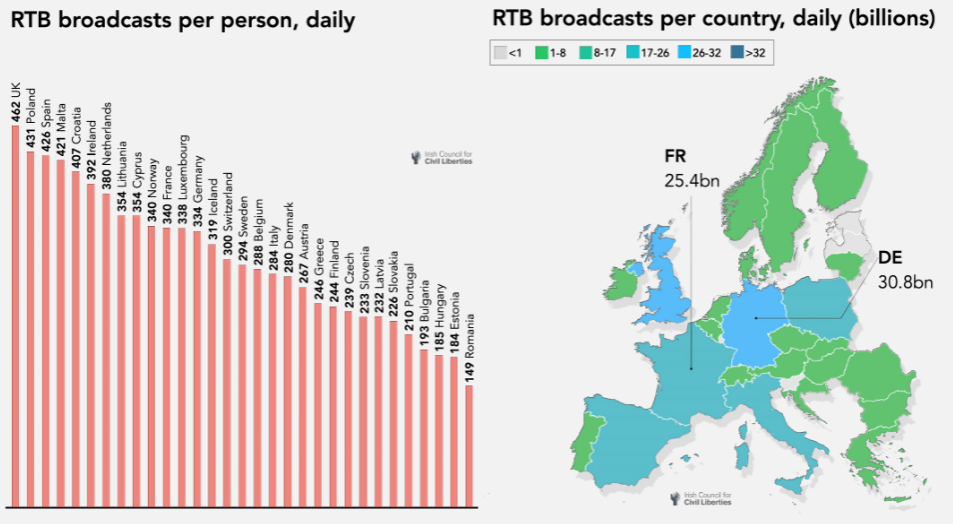
Number of RTB broadcasts by European country. Source: »Europe’s hidden security crisis« report, 2023.
But what is important to know is, that RTB technology is active on practically all websites and mobile applications, where it collects literally huge amounts of personal data about users. Google’s RTB system, which is currently the largest, is active on 15.6 million websites and millions of mobile applications. And it transfers data about what users do on websites and how they use mobile applications 42 billion times (!) a day. Every day. And Google is “responsible” for only 21% of RTB downloads in the EU. To be more precise, this means that the RTB networks will collect data about the average German user once per a minute, while the online activities and locations of the average user in France will be transmitted to the RTB networks 340 times a day. Data for Slovenia show that for the average Slovenian user there are 233 such broadcasts per day.
AdInt
Unfortunately, the story does not end here, but actually just begins.
In September of this year, the Israeli media outlet Haaretz published an article in which they revealed that Israeli companies that develop and market cyber-espionage technologies have developed technology that allows spying on virtually anyone in the world by abusing the global advertising system. Israeli companies are said to have developed ad-spying technology, so called AdInt (advertising-based intelligence), which can not only monitor activities of individuals, but can also hack into their phones and computers. According to Haaretz, there is no defense against this, and at the time of publication of the article, at least one of the identified companies (named Insanet) had already sold the technology to one of the non-democratic countries. Money knows no borders, of course.
Haaretz did not publish many technical details about this in September, and their article went relatively unnoticed by the public. However, security experts at that time suspected, that the Israelis were using advertising networks both as a system for identifying targets and as a delivery system for delivering malicious software to phones. And when they manage to install Pegasus or Predator spyware on the victim’s phone through very targeted advertising, they can learn practically everything about the target. Where exactly the person is moving, with who they talk and about what, what e-mails do they write, what passwords they have, and, of course, obtain copies of all photos and documents from their phone. Or a computer.
Patternz
An then, in September of this year, the Irish Council for Civil Liberties published the report titled Europe’s hidden security crisis, in which it revealed additional dimensions of this type of surveillance.
The report revealed how private companies that sell cyber surveillance and espionage services use (or rather: abuse) RTB data. Virtually anyone can get an access to RTB data. RTB data is exported without any limits to countries such as China and Russia. Of course, not directly to government agencies, but private companies from these countries can get them, and we can only imagine what these companies then do with the purchased data. According to the Irish Council for Civil Liberties, Russian companies are, among other things, buying from Google the profiles of Russian Internet users who visit Russian opposition websites abroad. Probably for marketing purposes only.
But the access to the data also have private companies that are directly involved in surveillance and intelligence. The report cites examples of two such companies registering as an advertiser (actually they are called Demand Side Platforms or DSP’s), which enables them to obtain advertising data directly from providers. The company Rayzone is offering »mass collection of all internet users in a country« while the company Near Intelligence claims to have profile data on 152 million Europeans, including the identified location of their home, workplace and places they visit frequent.
But one of the most interesting is a private company ISA, Israeli Security Academy & technologies. The company developed Patternz, a tool that uses RTB data to profile 5 billion individuals, also targeting children of their targets. The tool enables an overview of the current and past locations of the targeted individual, information about whom the person has often met, and can automatically identify his children, spouses, colleagues and where the person usually moves. And of course - Patternz also claimed in its promotional material that they can conduct targeted attacks on individuals by sending “targeted messages, ads or malware directly through an ad network”. Patternz is closely associated with the Israeli advertising company NUVIAD, which is also registered as a DSP and in 2020 it has been receiving RTB data from Google, MobPub (Twitter), AOL/Yahoo, Smaato, OpenX, Amobee, Pulsepoint, Rubicon, Inneractive /Fyber (Digital Turbine), Opera Mediaworks, etc…
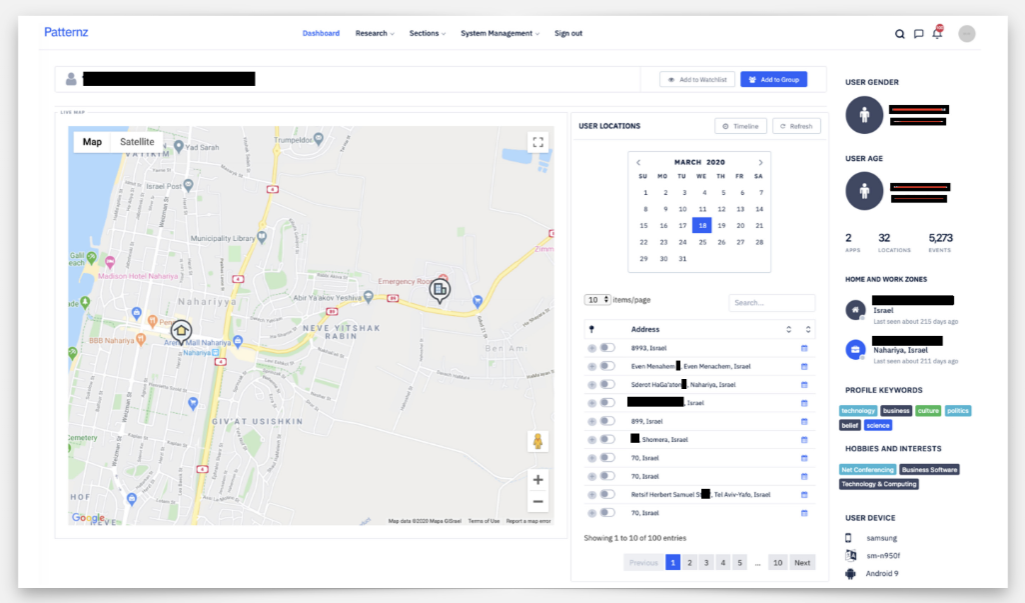
Patternz user interface. Source: »Europe’s hidden security crisis« report, 2023.
But the intertwining of the advertising and espionage sectors does not end here. NUVIAD is also associated with other cyber espionage companies. In 2017, the director of NUVIAD joined the board of directors of the Israeli company Ability, which is specialized in offering services for the interception of telephone communications.
The Patternz solution is also sold by the Singaporean company called Sovereign Systems. This company gained public attention in 2021 when media revealed that it had sold wiretapping equipment to Bangladesh, a country that has no diplomatic ties with Israel and even bans its citizens from travelling to Israel and doing business with Israeli companies. And where did Sovereign Systems get the equipment they sold to Bangladesh? Of course, in Israel. This has been openly admitted by the director of Sovereign Systems, James Moloney, who stated to the media that his company is just a front company for the Israeli’s PicSix. In 2018, the training of Bangladeshi intelligence officers was carried out by Israeli intelligence experts in Hungary, where they demonstrated live eavesdropping. Of course, without any legal basis and on randomly selected targets in Hungary. When money and “higher interests” are at stake, human rights are not important.
Kompromat
The question that naturally arises now is, who are the main targets of these tools? As analysis by the Irish Council for Civil Liberties shows, that one of the important targets are European political decision-makers and employees in sensitive jobs. This is clearly evident from the RTB profiles, which are, for example: “Government - Intelligence And Couterterrorism”, “Government - National Security and International”, “Person being in procurement Aerospace and Defence sector”, “People who work in the military”, “People working in judiciary” and “Decision makers for the Government” in France and Germany. And “Employees in the field of nuclear energy”. And “Decision makers in political organizations”. Of course, in each European country separately. And so on, and so on. All the way to “Military spouses and family”.
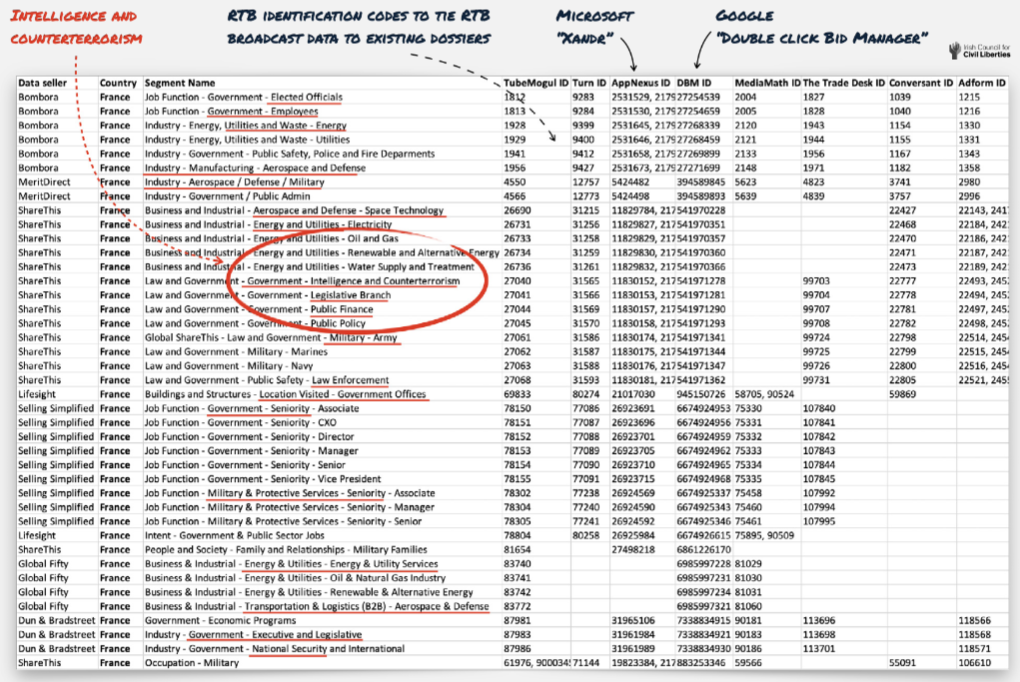
User segmentation in the RTB system. Source: »Europe’s hidden security crisis« report, 2023.
And this profiling is not only one-dimensional, but is also includes psychological profiling. Analytics tools are used to identify people with financial problems, people with mental health problems or vulnerabilities, their sexual preferences, and even whether they have ever experienced sexual abuse in the past.
At this point, it is time to open the dictionary and look for the word “kompromat”. Kompromat is short for “compromising material”, that is, harmful information about someone that can be used to create negative publicity or for blackmail. The word originates from the Russian language, came into public use in Soviet times, and its exact origin is from the jargon of the Soviet secret police from the 1930’s. Wikipedia gives a rather comprehensive definition of the word: “disparaging information that can be collected, stored, traded, or used strategically across all domains: political, electoral, legal, professional, judicial, media, and business”. And it adds that Kompromat does not necessarily target individuals or groups, but rather collects information that could be useful at a later time.
If the global advertising system smells like Soviet times to you, you are not the only one. And if you now remembered Stalin, his secret police, purges and gulags, you are also not the only one.
RTB data, which seems to be systematically collected by certain private organizations engaged in cyber surveillance and espionage, can most accurately be described with the word kompromat. Especially since it involves the systematic collection of data on financial status, mental and physical health, and the most intimate secrets of European leaders and employees of European critical infrastructure. This exposes European institutions and industry to hacking, extortion and compromise, which in fact undermines European security.
And you?
If you still believe that you are too insignificant to be the target of such surveillance, and that you have nothing to hide anyway, remember that you do not need to be in the category of political decision-makers or employees of critical infrastructure. It is enough that one of the “persons of interest” is your colleague, friend or neighbour. Or his son attends the same kindergarten as your daughter. And it is not necessary that this person is a high-ranking political official, a judge or a director of a strategic company. She may only be in charge of public procurement, or he may have access to some interesting information due to his function.
Perhaps you have now thought that it would be a good idea to delete your browser history. Let us tell you a secret. It has long been too late for that. Ad networks have remembered more of your browsing history than you or your browser. They remember which apps you use, and where you have physically been in the past. You also have no control over whether your data will be sent to intelligence companies or secret services. The genie is already out of the bottle. You can only hope that you will not suffer the same fate as that unfortunate priest from the beginning of this article.
Article has been published in Sobotna priloga. Full text in Slovenian language is also available.
Ključne besede: prestrezanje, nadzor